Android Antivirus 2018 Free (Review or Test or Eval)
- Tested Products
- Test Results
Introduction
AV-Comparatives' 2017 test of Android antivirus products was inspired past the discovery of an Android app called Virus Shield, which claimed to scan mobile devices for malware, merely in fact did nil of the sort. In reality, running the app just showed a progress bar, supposed to represent browse progress, followed by an annunciation at the end of the "scan" that the device was free of malicious apps. Worryingly, the app had been available on the Google Play Store, and thousands of users had paid money for it (although this was ultimately refunded to them by Google).
Unfortunately, more dubious antivirus apps – ones which announced not to offer any protection at all – have appeared since then. In Jan 2018, Sophos' NakedSecurity weblog reported that a new dubious antivirus app for Android was available from the Google Play Store. The article claimed that the app in question, Super Antivirus 2018, was equally ineffective at blocking malware every bit was Virus Shield, but was more than sophisticated in its study of apps that had been "scanned".
It is clear that dubious antivirus apps for Android accept not gone away, and users should be on their guard against such tricks. Last year'south test demonstrated that there are also some Android security products that are non deliberately deceptive, but are ineffective at protecting the device confronting malware. Of the 100 products tested last twelvemonth, roughly a quarter detected 100% of the malicious apps, but a similar number identified less than 30% of the samples.
To help owners of Android devices to distinguish betwixt genuine and effective Android antivirus apps on the 1 hand, and dubious/ineffective ones on the other, AV-Comparatives take again tested the effectiveness of antimalware programs for Android, in the 2018 Android Test.
Tested Products
For this exam, we searched for and downloaded over 200 antimalware security apps by various different developers from the Google Play Shop.
The following 84 apps detected over xxx% of malicious apps, and had zip fake alarms:
| 7Labs Antivirus & Security | Spotter Antivirus & Security |
| AegisLab Antivirus Premium | MalwareBytes Anti-Malware |
| AhnLab V3 Mobile Security | Max Mobi Secure Full Security |
| Ali MoneyShield | McAfee Security & Antivirus |
| Antiy AVL | MobiDev Studio Antivirus |
| Ariasecure Bornaria security | MobileAppDev Virus Cleaner |
| Avast Mobile Security & Antivirus | NEWAPPSDEV SmadAV |
| AVG Antivirus Free | newborntown Solo Security |
| AVIRA Antivirus Security | NightCorp Super Antivirus |
| Baidu DU Antivirus Mobile Security & AppLock | NortonMobile Norton Antivirus & Security |
| BaiSi Mobile Antivirus | NQ Mobile Security & Antivirus |
| BangStudio Virus Cleaner | One App Super Make clean Speed Security MAX |
| Bastiv Security Antivirus | Panda Complimentary Antivirus |
| Best Tools Pro Cleaner | PCVARK Falcon Mobi Cleaner |
| Bitdefender Mobile Security & Antivirus | Photo Editor Creative Cleaner |
| BullGuard Mobile Security and Antivirus | PICOO Design Ability Antivirus |
| Check Point ZoneAlarm Mobile Security | Ability Tools Team Mobile Security |
| Cheetah Mobile CM Security CleanMaster | PSafe Antivirus |
| Chili Security Android Security | Qihoo 360 Mobile Security |
| Comodo Mobile Security | Quick Heal Antivirus & Mobile Security |
| Defenx Security Suite | REVE Antivirus Mobile Security |
| DevStudio99 Antivirus | Rising mobile security |
| PhysicianWeb Security Infinite | Security Apps Studio Virus Cleaner |
| Emsisoft Mobile Security | Security Cleaner Team ZoneX Security |
| eScan Mobile Security | Security Aristocracy Antivirus |
| ESET Mobile Security & Antivirus | Security Mobile Max Clean |
| ESTsoft ALYac Android | Security Safe Protect Squad Super Virus Cleaner |
| Fast Runway Super Security Complimentary AntiVirus | Sophos Complimentary Antivirus and Security |
| F-Secure Mobile Security | Tencent WeSecure Antivirus |
| G Information Cyberspace Security | TG Soft VirIT Mobile Security |
| GearMedia G-Antivirus Security Pro | ThreatTrack VIPRE Mobile Security |
| GizmoLife GizmoSafe Antivirus | ToolsDevelope Antivirus |
| Google Play Protect | Trend Micro Mobile Security & Antivirus |
| How-do-you-do Dev Squad Security Antivirus & Privacy | TrustGo Antivirus & Mobile Security |
| High Security Team Antivirus | Trustlook Premium Mobile Antivirus |
| Himlamo Super Antivirus | Vitekco 1000 Antivirus |
| Hyper Speed Antivirus | Webroot Security Premier |
| Ikarus mobile.security | Wecool Ballsy Secuity |
| IntelliAV Anti-Virus | WhiteArmor Security Pro |
| K7 Mobile Security | Z Lock Screen Squad Antivirus |
| Kaspersky Antivirus & Security | Zemana Mobile Antivirus |
| LBE Security Chief | ZONER Mobile Security |
The antimalware apps from the post-obit 79 vendors detected less than 30% of the Android malware samples, or had a very high simulated alarm charge per unit on popular clean files from the Google Play Store: AndroHelm, ANTI VIRUS Security, ARSdev, AVC Security Joint Stock Visitor, AZ Super Tools, Birdie Antivirus, Best Apps Drove, BKAV, Booster Antivirus, Brainiacs Apps, Bsafe Labs, BSM SECURITY, CA Uber Apps, chkitham, CHOMAR, devapp81, Ellena Rehman, Fast Tool Mobile Apps, fluer-apps.com, Gamma+ Labs, Glagah Studio, Become Security, Gotechgo, GPaddy, AV Antivirus Security Ltd, Green Booster, H2, Militarist App, Hornet Mobile Security, Iobit, ITIanz iT Solution, Itus Mobile Security, Kara Inc., K-TEC Inc., lal bazai, LINE, looptop, Master VPN, Max Antivirus Lab, Max Security, Mobi Fox, MobiCluster, MSYSOFT APPS, Muel Dev., My Android Antivirus, NCN-NetConsulting Ges.chiliad.b.H., NetLink, NOAH Security, Nozzle Ltd, NP Mobile Security, Octa apps, OG Kush, Oriwa, Power Antivirus, Pro Tool Apps, Puce, Radiant Apps World, Rgamewallpaper, Security & Antivirus for Android, Security and Protector for Mobile, ShieldApps, But Fantabulous, smallapp, SmartToolsApps, Super Security, TAPI Security Labs, Topi Maxi Group, ToTo Studio, TransApp, UFGAMES, Vasa Pvt Ltd, VSAR, W4VN Team, We Make Information technology Appen, Wingle Apps, Womboid Systems, xplus apps, ZeroApp Ltd., and Zillya! Mobile.
We consider those apps to be risky, equally they are either dubious/deceptive or dangerous/ineffective. In a few cases the apps are simply buggy, e.g. because they have poorly implemented a third-political party engine. Some apps are conspicuously dubious, detecting only a handful of very sometime Android malware samples, and assuasive all apps which contain certain strings, making them likely to pass some quick checks and thus be accustomed by the app stores.
A number of the in a higher place apps take in the meantime already been recognized as Dubious AVs/Trojans/PUA by several reputable mobile security apps – it is to exist expected that Google will remove nearly of them from the Google Play Store in the upcoming months (and hopefully enhance their verification checks, thus blocking other such apps from the store). We would recommend the vendors concerned to remove their apps from the store until they tin provide genuine and reliable protection.
The antimalware apps of the post-obit 41 vendors take in the meantime (in the last two months) been removed from the Play Store: androiddeve, Antivirus inc, App-lab, AppsGesture, BestCode, Bethanyzrqcr Zimmermanzisr, Devo669kaptchiia, Diana Randall, DIMOgamesL, Gayle Billick, GoLogix, Joanwy Hartmanebe, JRMedia, katana apps, LHC Lab, Lopez ops Dev Ap Hirox, Millicent Whitehead, Mobile Solution: Antivirus Security, Mobilead Inc., MPSecurityLabs, MtStudio, NCK Corp, now King Apps, Octappis, Ostro Apps, Plus App, prodev2017, Security Lab, Shreeji Tech World, Simple Soft Alliance, SoHDev, Solo Antivirus, SPAMfighter aps, SuperApps Dev GmBH, Superozity, Organisation Security Inc, Tools Security for Mobile, Toolsdev, Total Defense, Uptotop33, and Zexa Software.
Most of the apps removed, as well equally the very buggy, unsafe and ineffective apps, announced to accept been adult either by amateur programmers or by software manufacturers that are not focused on the security business. Examples of the latter category are developers who make all kinds of apps, are in the advertising/monetization business organization, or just want to have an Android protection app in their portfolio for publicity reasons. Apps made past amateurs can be oft spotted in the Google Play Store by looking at the options for contacting the authors. Typically, hobby developers volition non provide a website address, only an e-mail accost (commonly Gmail, Yahoo, etc.). Additionally, most such apps practise not provide whatsoever sort of privacy policy. Google tries to purge from the Play Shop all apps which lack a privacy policy, which helps to get rid of some low-quality apps. Of grade, i should bear in heed that not all apps fabricated by amateur developers are necessarily ineffective.
Exam Procedure
Description of test system
The Android security solutions tested were checked for their efficacy in protecting against the 2,000 most common Android malware threats of 2017. Manually testing 200+ security products against two,000 malicious apps is not practicable. Considering of this, the examination was run on our automated Android testing framework.
Even though the testing process is automated, the framework realistically simulates real-world conditions. This includes testing on concrete Android devices (as opposed to emulators), every bit well every bit simulation of realistic device usage patterns.
The framework consists of two components: a client app on each of the test devices, and a server application. The client app monitors the status of the device and sends its findings to the server at the end of a exam case, to document the testing procedure. The customer monitors file and process changes, newly installed apps and their permissions, as well as reactions of the installed security software to malicious activities on the device. The server remotely controls the exam devices via WiFi and organizes the results received by the client applications.
The system scales well with the number of continued clients. This allows a big number of security products to be tested in parallel. To ensure even chances for all participating products, connected clients can be synchronized to commencement the execution of a exam case at the same fourth dimension. This is especially important for testing recent malware samples, which security vendors may non have encountered all the same.
Methodology
The test was performed in Jan 2018, on Nexus 5 devices running Android 6.0.1 ("Marshmallow"). Each security app was installed on a separate physical exam device. Earlier the exam was started, the software testbed on all exam devices – Android itself, stock Android apps, plus testing-specific third-political party apps – was updated. Later this, automatic updates were switched off, thus freezing the state of the test system. Next, the security apps to be tested were installed and started on their corresponding devices, updated to the latest version where applicable, and the malware definitions brought fully up to engagement.
If any security application encouraged the user to perform sure actions to secure the device, such equally running an initial browse, these actions were performed. If the application offered to activate additional protection functions such as on-install scanning, cloud protection, or detection of Potentially Unwanted Applications (PUA), these features were activated likewise. To ensure that all security products could access their respective cloud analysis services, each device was continued to the Net via a WiFi connectedness.
One time these steps were taken, a clean snapshot of each device's storage was created, and the exam was started.
Each test case was conducted using the aforementioned process:
- Open up the Chrome browser and download the malicious sample
- Open the downloaded .apk file using a file explorer app
- Install the malicious app
- Execute the installed app
Subsequently each of the above steps, the installed security awarding was granted enough time to analyze the malicious sample and notify the user of malicious activity on the device.
If, at whatsoever point during the execution of a examination example, the installed antivirus application detected and blocked the malicious sample, the sample was considered "detected" and the test case was concluded (apps detected after installation were non executed, for instance).
At the end of each test example, the device was reset to a clean land. If the malicious sample had non been executed on the device, the sample was uninstalled and/or deleted from the device storage. If the malicious sample had been run, the clean device snapshot was restored before starting the next exam case.
When computing the protection score for each product, nosotros did not consider at which phase a malware sample was blocked, i.e. whether it was blocked on download, on installation or on execution. The just factor influencing the protection charge per unit is whether the security solution protected the device from being compromised by the malicious sample.
A bones faux-alarm test was done, only to check that none of the antimalware products "protects" the system by simply identifying all apps as malicious. Several shady and depression-quality apps detected as malware a number of the 50 clean and popular apps from the Google Play Shop.
Testcases
For this test, the 2,000 well-nigh mutual Android malware threats of 2017 were used. With such samples, detection rates of between 90% and 100% should be easily accomplished by 18-carat and effective antimalware apps.
| Number of tested apps | 204 |
| Number of tested malicious APKs | 2000 |
| Number of tested clean APKs | 50 |
In total, around 400,000 test runs were performed for this report.
Examination Results
| Vendor | % |
| AegisLab | 100% |
| AhnLab | |
| Alibaba | |
| Antiy | |
| Avast | |
| AVG | |
| AVIRA | |
| Baidu DU Apps | |
| BaiSi | |
| Bitdefender | |
| BullGuard | |
| CheckPoint | |
| PhysicianWeb | |
| Emsisoft | |
| ESET | |
| F-Secure | |
| G DATA | |
| Kaspersky Lab | |
| McAfee | |
| Norton Mobile | |
| PCVARK | |
| Quick Heal | |
| Security Mobile | |
| Security Safe Protect | |
| Sophos | |
| Tencent | |
| Trend Micro | |
| TrustGo | |
| ESTsoft | 99.9% |
| Ikarus | |
| Webroot | 99.seven% |
| Ariasecure | 99.5% |
| Qihoo 360 | 99.3% |
| IntelliAV | 99.two% |
| K7 | |
| eScan | 99.0% |
| Bastiv | 98.8% |
| VIPRE | |
| REVE | 98.seven% |
| Security Apps Studio | 98.iv% |
| WhiteArmor | 98.three% |
| Chili Security | 98.ane% |
| PSafe | 98.0% |
| Hullo Dev | 97.3% |
| Chetah Mobile | 96.two% |
| Panda | 95.7% |
| Comodo | 94.5% |
| Lookout | 93.9% |
| Vendor | % |
| Fast Track | 93.4% |
| Hyper Speed | |
| LBE | |
| One App | |
| Photo Editor Creative | |
| Power Tools Team | |
| Security Elite | |
| Wecool | |
| BangStudio | 92.5% |
| MalwareBytes | 87.2% |
| Max Mobi Secure | 82.vii% |
| TG Soft | 82.one% |
| Zemana | 78.8% |
| Rising | 78.1% |
| Google Play Protect | 75.3% |
| GizmoLife | 73.2% |
| Defenx | 70.iv% |
| Best Tools Pro | 63.ix% |
| DevStudio99 | |
| MobileAppDev | |
| MobiDev Studio | |
| ToolsDevelope | |
| Z Lock Screen Team | |
| NQ | 55.ane% |
| Trustlook | 51.4% |
| Himlamo | 44.half-dozen% |
| NEWAPPSDEV | |
| NightCorp | |
| 7Labs | 44.iv% |
| GearMedia | |
| Loftier Security Team | |
| Vitekco | |
| Security Clean Team | 43.8% |
| newborntown | |
| PICOO Design | 43.6% |
| ZONER | 37.half dozen% |
The table above shows the protection rates reached by the 84 products that blocked over 30% of samples. We consider apps that cake less than 30% of common Android threats (listed on page 4) to be unsafe to use.
Anti-malware apps detecting under 30% of the ii,000 malicious Android apps are not listed in the chart above – partly for display reasons, merely too because nosotros consider them ineffective and unsafe.
Notes
Some products make use of other vendors' engines (see examples below). While some score the aforementioned as the engine vendor's own product, some exercise not. According to the licensing developers, this may exist caused past several factors, such every bit different internal settings used by the third-party apps, the utilise of older engines or different secondary engines, engine implementation and bugs.
- Cheetah Mobile uses an Antiy engine for "heuristic" scans (deactivated by default). The English language/International version of Cheetah Mobile would have scored 100% if the "heuristic" engine had been activated. The Chinese version appears to have a bug in the implementation of the Antiy engine.
- CA Uber, Fast Track, Hyper Speed, IOBit, LBE, ONE App, Photo Editor Artistic, Ability Tools Team, Security Aristocracy, WeCool Security, WeMakeItAppen, and Womboid Studio employ the OpenAVL scan engine of Antiy. The quality of the engine implementation varies amid the apps.
- Security Mobile and Security Safe Protect use the Tencent scan engine.
- AVG and PSafe use the Avast Qihoo is a major investor in PSafe.
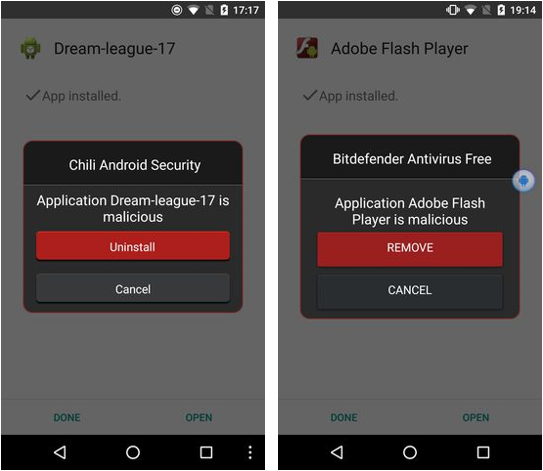
- Chili Security and Emsisoft use an engine made by The Chili Securityapp is basically a rebranded version of an older Bitdefender mobile product – encounter screenshots below:
During our exam, we found that quite a few apps seem to be closely related variants of the same matter, or use a common "AV app template". In some cases, only the proper noun, logo and colour scheme are different. Examples are shown beneath:
- 7Labs, GearMedia, High Security Team, Himlamo, NEWAPPSDEV, NightCorp and Vitekco:

- Best Tools Pro, DevStudio99, MobiDev Studio, MobileAppDev, ToolsDevelope Inc, Z Lock Screen Squad:

- Become Dev Squad, newborntown, Power Antivirus Security, Security Cleaner Team:

- Hyper Speed, ONE App Ltd., Ability Tools Team:

- AZ Super Tools, GPaddy Mobile Security, Principal VPN, Mobile Antivirus & Security by Netlink, Puce Ltd, Topi Maxi Group, W4VN Team (all of which blocked nether 30% of samples):

- Security Elite, Wecool Security Lab

Risky Security Apps
As mentioned in the Tested Products section, some apps were not included in the results table, because nosotros consider them risky. About half of those apps were excluded considering of their low malware detection capabilities. The other one-half blocked many of the malicious samples used in the test, merely should in our opinion notwithstanding be considered risky; in the section below, we explain why nosotros came to this conclusion.
When opening the packet files of any of those apps, one can find a suspicious text file in the "assets" subfolder named "whiteList.json". The following effigy shows some of the content of this file:
{ "data": [ { "packageName": "com.google.android.*" }, { "packageName": "com.adobe.*" }, { "packageName": "com.booking" }, { "packageName": "com.facebook.*" }, { "packageName": "com.instagram.*" }, { "packageName": "com.twitter.*" }, { "packageName": "com.whatsapp" }, [...] ] } The content of the "whiteList.json" file is consequent with the results we institute during our simulated-positive tests: all apps whose bundle proper name match this white-list are considered "trusted applications" past these "AV apps". For example, the whitelisted parcel name "com.adobe.*", matches all packages, whose names showtime with "com.adobe.". While this entry means that all 18-carat apps made by Adobe (such as the Acrobat Reader app) volition be regarded as safety, this mechanism also allows whatsoever malicious app to bypass the security scan, simply past using "com.adobe.*" as its package name.
Apart from the apps on their respective whitelists, the risky "AV apps" cake almost all other apps, regardless of whether they were installed from the official Google Play Store or non. Some of them do not even carp to add together their ain packages to their whitelists, and so even block their own app. If using such an AV app, users can never be certain if whatsoever of the other apps on their device are actually malicious, because of the AV app's "block unless whitelisted" policy. Therefore, we do not consider the protection capabilities of these apps to be advisable.
In addition to using the same "detection" mechanisms, the user interfaces of these apps wait very similar too. Oft only differing in color, the apps in this category mainly use 1 of just a few different layouts:

We consider the apps made by the post-obit 38 developers to be deceptive: AV Antivirus Security Ltd, AVC Security, All-time Apps Collection, Booster Antivirus, BSM SECURITY, chkitham, Ellena Rehman, Gamma+ Labs, Glagah Studio, Gotechgo, Green Booster, ITIanz iT Solution, lal bazai, Kara Inc, looptoop, MobiCluster, Mobi Play tricks, MSYSOFT APPS, Muel Dev, NOAH Security, Nozzle Ltd, NP Mobile Security, Octa apps, OG Kush, Oriwa, Radiant Apps World, Rgamewallpaper, Security & Antivirus for Android, Only Fantabulous, smallapp, SmartToolsApps, Super Security, ToTo Studio, TransApp, UFGAMES, Wingle Apps, xplus apps, and ZeroApp Ltd.
Conclusion
Some of the Android security products in our examination blocked so few of the malware samples– in some cases literally none – that they cannot exist recommended as anti-malware apps. Additionally, this year we saw a large increase in apps that apply questionable detection mechanisms. Combining ineffective and risky anti-malware apps, we consider the majority of the exam apps to be unsafe to utilise.
Some of the apps that were ineffective at blocking malware may accept been abandoned by the developer and are thus no longer being updated in the Google Play Store. Whilst such cases cannot be regarded every bit scams, nosotros consider it irresponsible of the developers not to remove these apps from the Shop.
A few products from relatively well-known vendors did not score very well. Information technology is possible that the manufacturers have developed them purely for marketing reasons. That is to say, there is not much money in the Android security-app market, but having an Android app visible in the Google Play Shop helps to keep the vendor visible, and may thus promote their other, more profitable products such equally Windows security programs.
28 of the products we tested detected 100% of the malware samples; considering that the most common malicious Android apps of 2017 were used, this is what they should practice. Most of the vendors that usually take part in independent tests score highly, as their products are regularly scrutinised, and they actively develop them to ensure they are effective.
When information technology comes to choosing an Android security app, we recommend considering the post-obit factors. Using user ratings is clearly non effective, every bit the vast bulk of users will give their rating based solely on the user experience, without having any thought equally to whether the app offers effective protection. Some other reviews will have been faked by developers. Most of the 200 apps nosotros looked at had a review score of four or higher on the Google Play Shop. Similarly, the number of downloads can but be a very rough guide; a successful scam app may be downloaded many times before information technology is found to be dubious. Using well-known and reputable, verified vendors is recommended. As well equally participating in tests by independent test institutes, such vendors will have a professional website with contact information and a privacy policy. Information technology should also be possible to attempt the app – typically a few weeks' trial use is allowed – before purchasing. Users tin can and then assess the usability and any additional features of the production. A number of vendors make very constructive free versions of their apps; mostly these are more likely to display advertizing than the paid version, though this is not e'er the case.
For additional Android security app tests and reviews, please run across:
https://www.av-comparatives.org/mobile-security/
Copyright and Disclaimer
This publication is Copyright © 2018 by AV-Comparatives ®. Any utilise of the results, etc. in whole or in office, is ONLY permitted subsequently the explicit written agreement of the management board of AV-Comparatives prior to any publication. AV-Comparatives and its testers cannot be held liable for any damage or loss, which might occur every bit event of, or in connection with, the use of the data provided in this paper. We take every possible care to ensure the correctness of the basic data, only a liability for the correctness of the test results cannot be taken by any representative of AV-Comparatives. We do not requite whatsoever guarantee of the correctness, completeness, or suitability for a specific purpose of whatever of the information/content provided at whatever given time. No ane else involved in creating, producing or delivering examination results shall exist liable for whatever indirect, special or consequential damage, or loss of profits, arising out of, or related to, the apply or disability to utilise, the services provided by the website, exam documents or whatsoever related information.
For more information virtually AV-Comparatives and the testing methodologies, please visit our website.
AV-Comparatives
(March 2018)
Source: https://www.av-comparatives.org/tests/android-test-2018-200-apps/


0 Response to "Android Antivirus 2018 Free (Review or Test or Eval)"
Post a Comment